Data sovereignty is one of most critical issue related to cloud adoption. The main problem here it’s seems to be the lack of harmonious standards at international level, regional regulations and alliances or local laws. It is well known many national laws is permitting to local government authorities to access enterprise sensitive cloud data that become to be in conflict with the rights of data protection in the originating jurisdiction.
 Could be solved this apparent insurmountable gap? They are strategies that could reduce concerns related to data sovereignty. According Gartner research ”Five Cloud Data Residency Issues That Must Not be Ignored” enterprises should take only few steps to assure the privacy of sensitive information, achieve regulatory compliance and understand the implications of data disclosure laws. “Even if the data is encrypted and the keys are managed in a separate jurisdiction, enterprises should be aware that requests for legal assistance, based on bilateral agreements, may be executed between those countries,” says Gartner analysts. “However, in a well-architected system, the cloud application provider does not have direct access to the keys. In this way, if a legal request is made for access to the data, the enterprise must be involved.”
Could be solved this apparent insurmountable gap? They are strategies that could reduce concerns related to data sovereignty. According Gartner research ”Five Cloud Data Residency Issues That Must Not be Ignored” enterprises should take only few steps to assure the privacy of sensitive information, achieve regulatory compliance and understand the implications of data disclosure laws. “Even if the data is encrypted and the keys are managed in a separate jurisdiction, enterprises should be aware that requests for legal assistance, based on bilateral agreements, may be executed between those countries,” says Gartner analysts. “However, in a well-architected system, the cloud application provider does not have direct access to the keys. In this way, if a legal request is made for access to the data, the enterprise must be involved.”
Understanding the risks is the first step for any organization to become more proactive. Gartner research is recommending the following five steps to eliminate data sovereignty problems:
- Deploying encryption solutions is mandatory mainly if data residency is sensitive for data crossing borders
- Ensure that privileged users in cloud services providers are not granted access
- Manage the keys locally to comply with local privacy requirements
- Ensure that the selected vendors encryption products can provide the requested level of security
- Use a documented key revocation and destruction process
In the same time, “control, management, and visibility” are the top concerns when we are thinking to cloud data residency, according to GigaOM.
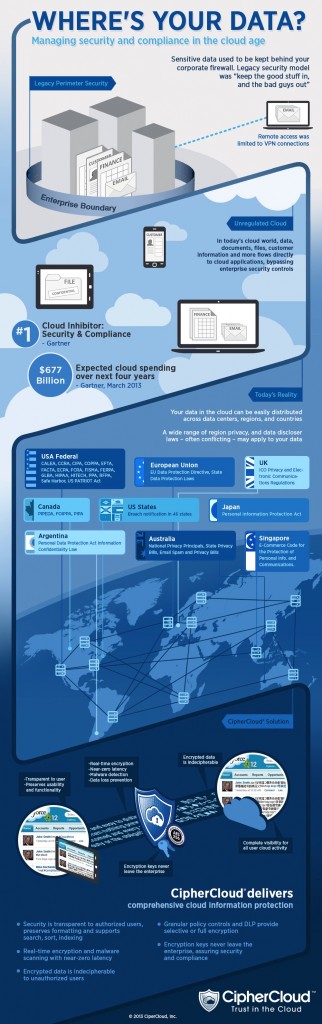
In attached Infographic CipherCloud is showing the main data residency regulation that could be in conflict for regional or multinational companies, and the elementary cloud security process that could be applied.
Source: CipherCloud


The NSA has proven that it really does not matter where your data is located. Internal private or external public cloud. If the NSA wants to snoop, steal, infect or destroy they can and will and there is nothing you can do about it. If they are capable their are others just as capable. Try as you might if someone wants to get to you they will. If your hope is to slow down mediocre hackers. The public cloud is probably better suited at protecting your data than a contingent of part time half witted IT security geeks, whose other job is watching blinking lights.